Hardly a day goes by without some news of a data breach affecting millions of people. Criminals seem adept at targeting and breaching large organizations, so you might think they’d leave small businesses alone.
Unfortunately, the opposite is true. Small businesses are at greater risk because they don’t have the resources to invest in the best protection. However, that doesn’t mean all’s lost. Much of the time, breaches occur because someone did something silly.
In this article, the SupportYourApp team discusses the top 10 mistakes people make when it comes to cybersecurity. No matter how advanced your security measures are, they may not be enough if you’re doing any of the following.
1. Neglect Software Updates
It’s difficult, if not impossible, for a software developer to produce a perfect product. Most rush their products to the market, and others only realize there are bugs after releasing the software. In other cases, bad actors develop new attack vectors that weren’t an issue at release.
Developers deal with this issue by issuing patches and updates. These plug security flaws and generally improve performance. If you don’t update the software, you’re leaving yourself vulnerable.
2. Use Weak or Repeated Passwords
We know that it’s challenging to remember a long list of passwords, but you can’t take chances. Hackers use malware that tries the most common combinations. The shorter and easier the password, the faster hackers crack it.
A good password contains about 16 characters. These should be a mix of special, upper, and lower case letters. You should avoid actual names or number sequences. If you’re concerned you won’t remember it, you can use a secure password manager.
Another issue is using the same password on multiple sites. Hackers attack less well-protected sites and then run credential-stuffing attacks on business and banking sites. This might enable them to gain access to better-protected sites.
3. Share Passwords or Credentials
Sharing passwords or log in credentials, whether via email, text, or other means, increases the risk of unauthorized access and compromise. You don’t know what someone else’s motives are.
4. Click on Suspicious Links or Attachments
You should never click on a link in an email or open an attachment unless you’re positive you know where it’s coming from. We’d take this a step further and suggest never clicking on links at all. Rather head over to the legitimate site and go from there.
Bad actors use this technique to embed malware or trick you into revealing your password.
5. Ignore Phishing Warning Signs
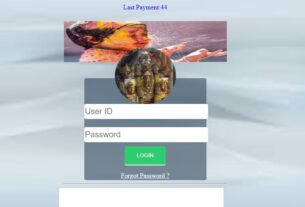
Phishing attacks take many forms and can be quite convincing. They may have an email address that looks like the real thing. The clues are always there, however. Phishers like to promote panic, so you’ll need to take immediate action.
Carefully read the email address because it’ll usually be slightly different from the real thing. If you’re concerned, navigate to the company’s site without clicking on the link and sign into your account.
The idea here is that they redirect you to a site that looks legit. You’ll then enter your username and password, and they’ll capture those details.
6. Disable Antivirus or Firewall Protection
There’s never any good reason to do this. You should leave this protection in place and update the antivirus regularly.
7. Use Unsecured Wi-Fi Networks
Public Wi-Fi networks put you at risk. Avoid them as much as possible. Alternatively, use a VPN service to protect your data if you must use them.
8. Store Sensitive Information Insecurely
You should encrypt sensitive information on all of your devices. This way, if there’s a breach, you can limit the damage it does.
9. Ignore Privacy Settings
Social media is a popular hunting ground for hackers. If you don’t enable your privacy settings properly, they’ll be able to mine a great deal of data. They look for things like your mother’s maiden name, pet’s name, and birth dates. These are all things that might answer the security questions.
10. Overlook Security Awareness Training
If you own a business, you can’t assume that your employees will be current with the latest security practices. Invest in security awareness training programs to educate users about common cyber threats.
Conclusion
Data is the gold of this century. Stop the gold rush by implementing some basic cybersecurity measures to protect your information. We all know the risks, but it’s helpful to go over them periodically.

James Oliver is a professional blogger and a seasoned Content writer for technologyspell.com. With a passion for simplifying technology and digital topics, he provides valuable insights to a diverse online audience. With four years of experience, James has polished his skills as a professional blogger.